The Yocto 1.7.1 (Dizzy branch) from Freescale source will be used for building a BSP for the i.MX 6 RIoTboard. The final image will consist of the following components
- U-Boot version 2014.10 from the Freescale git repositories.
- Linux kernel version 3.17.4 from the Freescale git repositories.
- ext3 root filesystem with selected packages
1. Add profiling tools and static development packages to image
First, add the following profiling tools contained within the tools-profile package to the final image. Add static versions of the development packages to the target image. Therefore, add the IMAGE_FEATURES line to bsec-image.bb as follows.
sources/meta-bsec/recipes-bsec/images/bsec-image.bb should contain the following
SUMMARY = "A small image just capable of allowing a device to boot."
IMAGE_INSTALL = "packagegroup-core-boot ${ROOTFS_PKGMANAGE_BOOTSTRAP} ${CORE_IMAGE_EXTRA_INSTALL}"
IMAGE_LINGUAS = " "
LICENSE = "MIT"
inherit core-image
IMAGE_FEATURES += " tools-profile staticdev-pkgs"
IMAGE_ROOTFS_SIZE ?= "8192"
2. Add bison, flex, and gnupg packages to image
Now add bison, flex, and gnupg to the list of packages installed to the target image.
Add the following line to bsec-image.bb after the IMAGE_FEATURES line as follows.
sources/meta-bsec/recipes-bsec/images/bsec-image.bb should contain the following
SUMMARY = "A small image just capable of allowing a device to boot."
IMAGE_INSTALL = "packagegroup-core-boot ${ROOTFS_PKGMANAGE_BOOTSTRAP} ${CORE_IMAGE_EXTRA_INSTALL}"
IMAGE_LINGUAS = " "
LICENSE = "MIT"
inherit core-image
IMAGE_FEATURES += " tools-profile staticdev-pkgs"
CORE_IMAGE_EXTRA_INSTALL += "bison flex gnupg"
IMAGE_ROOTFS_SIZE ?= "8192"
3. List available packages
The full list of available packages can be viewed by executing the following command
$ bitbake -s
4. Setup source code archiving for all packages contained within image
Next, archive the source code for all packages contained within the image.
This can be achieved by adding the following two lines to the end of the build/conf/local.conf file
INHERIT += "archiver"
ARCHIVER_MODE[src] = "original"
5. Ensure license files are archived and included with binaries.
Subsequently, ensure that the license files accompany each binary in the final image by adding the following two lines to the end of the build/conf/local.conf file.
COPY_LIC_MANIFEST = "1"
COPY_LIC_DIRS = "1"6. Add package testing to build
Now, add package testing to the build by adding the following two lines to bsec-image.bb
The contents of sources/meta-bsec/recipes-bsec/images/bsec-image.bb should be as follows
SUMMARY = "A small image just capable of allowing a device to boot."
IMAGE_INSTALL = "packagegroup-core-boot ${ROOTFS_PKGMANAGE_BOOTSTRAP} ${CORE_IMAGE_EXTRA_INSTALL}"
IMAGE_LINGUAS = " "
LICENSE = "MIT"
inherit core-image
IMAGE_FEATURES += " tools-profile staticdev-pkgs"
CORE_IMAGE_EXTRA_INSTALL += "bison flex gnupg"
DISTRO_FEATURES_append = " ptest"
EXTRA_IMAGE_FEATURES += "ptest-pkgs"
IMAGE_ROOTFS_SIZE ?= "8192"
7. Setup source code mirror so that package sources can be fetched from cache
Next, make sure that bitbake checks for all of the source tarballs in a local directory before going to the Internet to fetch them. This can be achieved by adding the following lines to the end of the build/conf/local.conf file.
SOURCE_MIRROR_URL ?= "file://${BSPDIR}/source-mirror/"
INHERIT += "own-mirrors"
8. Create shareable cache of git and svn backends
Finally, create a shareable cache of source code management backends by adding the following to the end of the build/conf/local.conf file.
BB_GENERATE_MIRROR_TARBALLS = “1”
After an initial build is performed, the directory contents of download/ can be recursively copied into source-mirror/ and the following line can be added to the end of the build/conf/local.conf file.
BB_NO_NETWORK = “1”Consequently, all future builds will not fetch anything from the Internet and all package sources will be obtained from the sources in source-mirror.
9. Kick off the build
Kick off the build as follows
$ cd $HOME/src/fsl-community-bsp
$ MACHINE=imx6dl-riotboard . ./setup-environment build
$ bitbake bsec-image10. Copy sources to mirror
Copy the sources from the downloads directory to source-mirror by executing the following commands
$ cd ..
$ cp -R downloads/*.* source-mirror/After the build is complete, the license file for each package will be contained within the appropriately named subdirectory of build/tmp/deploy/licenses
The image manifest file build/tmp/deploy/images/imx6dl-riotboard/bsec-image-imx6dl-riotboard.manifest will contain a list of package names and associated versions for each of the packages in the image.
11. Boot the custom distribution image
After the build is complete, write the image to an SD Card as follows
$ cd build/tmp/deploy/images/imx6dl-riotboard$ sudo umount /dev/sdX
$ sudo dd if=bsec-image-imx6dl-riotboard.sdcard of=/dev/sdb bs=1M
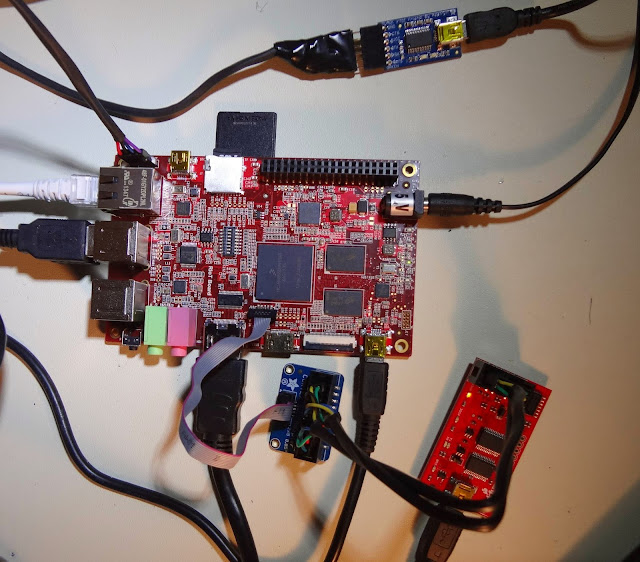
$ sudo syncInsert the SD Card in the J6 SD Card slot on the bottom of the RiOTboard, connect the board to the Host over Serial UART, run minicom at 115200,8N1 from a terminal on the Host, and power on the board.